Allow List Trusted IP Addresses
- Last updated
- Save as PDF
Gainsight NXT
This article helps admins restrict access to their Gainsight org and API connections by configuring trusted IP address ranges in Gainsight CS.
Overview
The Trusted Internet Protocol (IP) Ranges in Gainsight CS provide two levels of IP-based access control
- Application IPs: Restricting access to the entire Gainsight org
- Connectors IPs: Restricting access to specific API connections.
Admins can use either or both levels to enforce security policies.
Gainsight Mobile honors the trusted IP address range unless designated otherwise. To learn more about this configuration, refer to the Bypass Mobile section.
Set Up Application IP Ranges
The Application IP controls access to the Gainsight org as a whole. Once a trusted IP range is added, all access attempts from outside that range are blocked.
To add trusted IPs to the application:
- Navigate to Administration > Trusted IP Ranges. The Application IPs page appears.
- Click New to add the IPs. The Add IP Range dialog box appears.
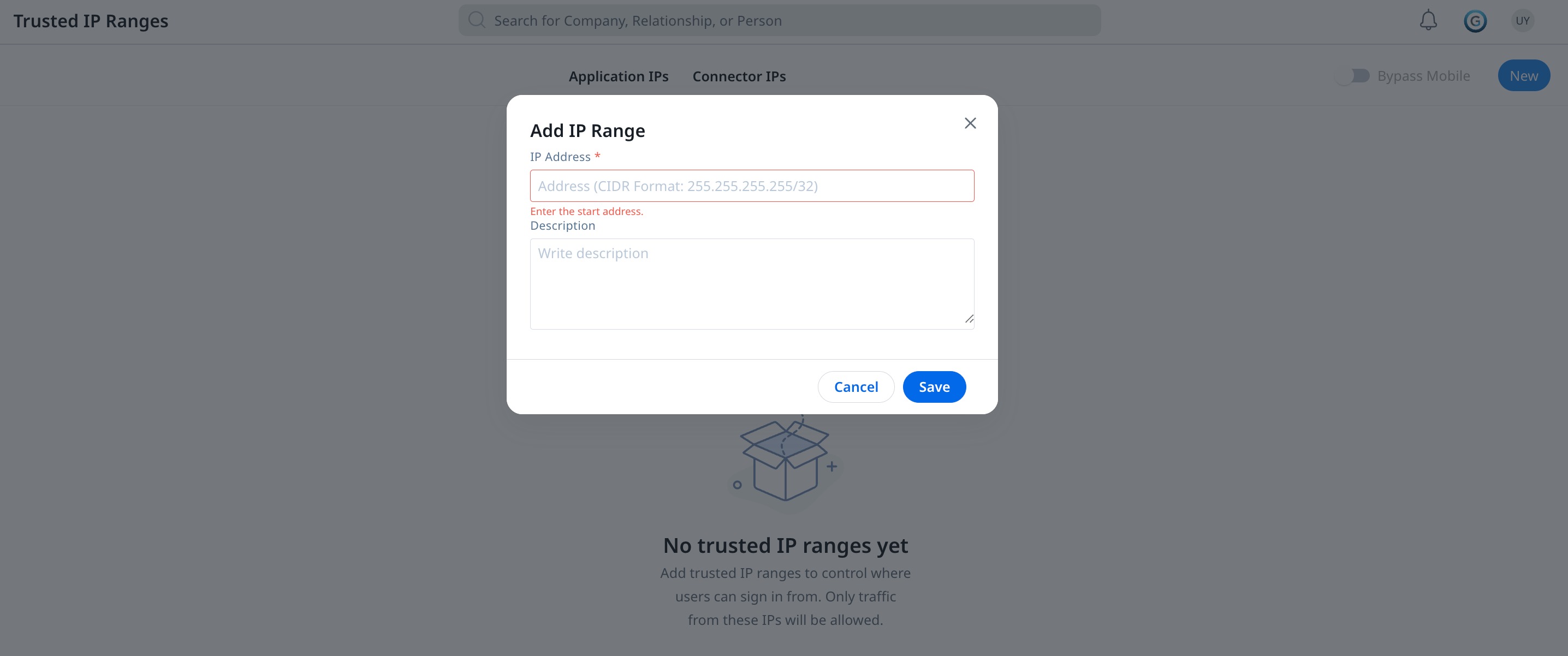
- In the IP Address field, enter the IP address or CIDR range. The desired format is indicated within the field.
- Click Save. The IP range is added as a trusted IP.
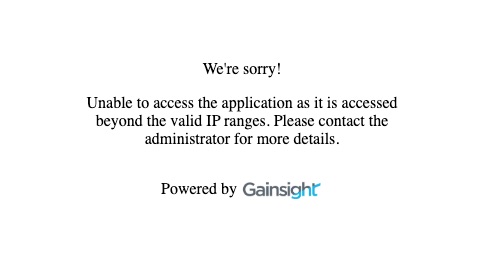
Once a network is added, users are unable to access the org from outside the trusted IP address range.
When someone attempts to access the org outside of the valid IP address range, the following message is displayed:
Configure Mobile Access
IP Allow lists configured in the web application are honored in Mobile. You can turn off this setting for mobile access.
To restrict IP access through mobile:
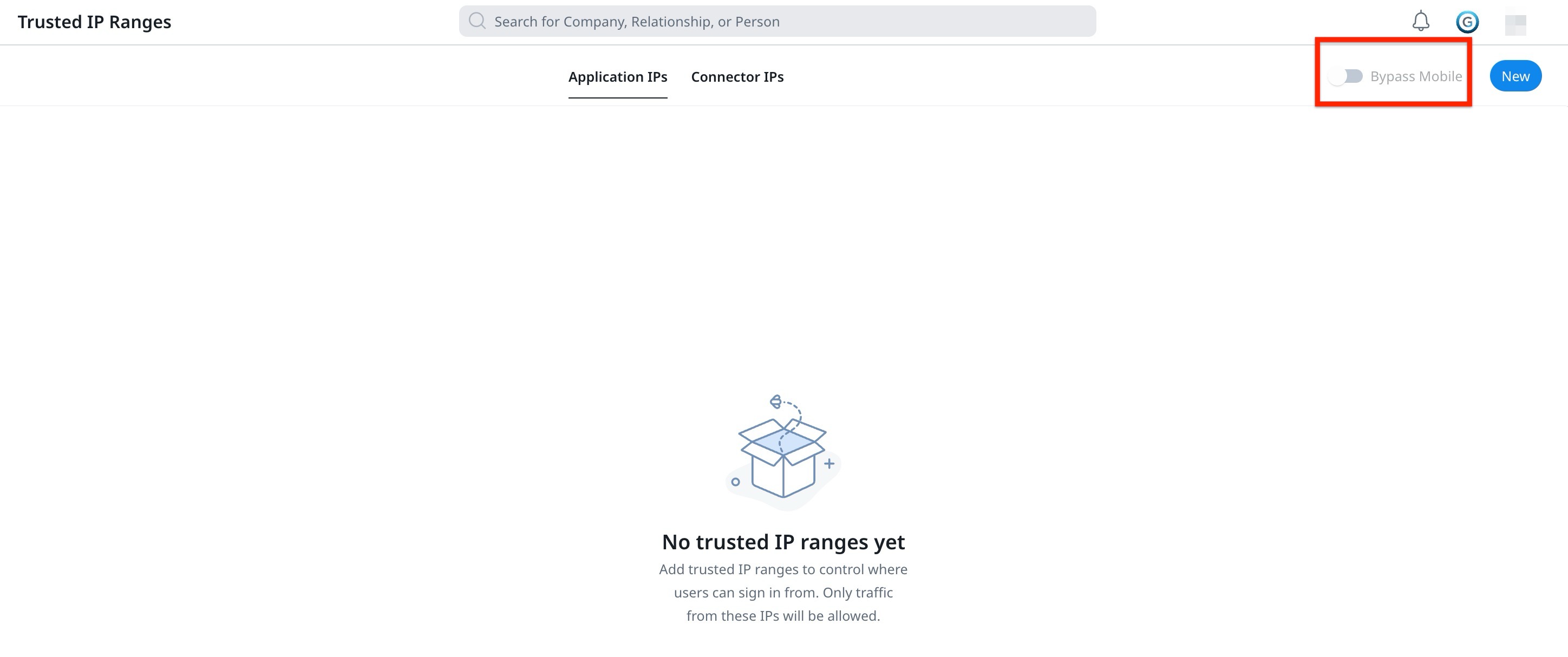
- Navigate to Administration > Trusted IP Ranges. The Application IPs page appears.
- Turn off the Bypass Mobile toggle. Mobile users are no longer restricted by the IP allow list.
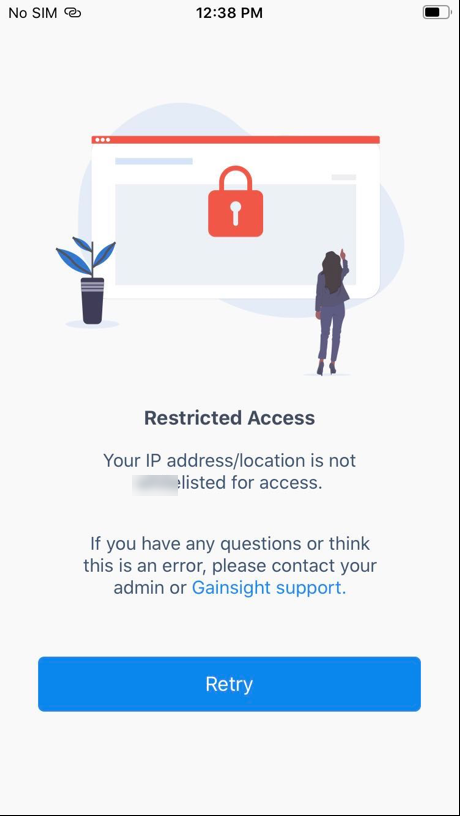
If Bypass Mobile is not toggled on, and a mobile user attempts to access the org outside of the valid IP address range, the following message is displayed:
Restrict Access to Specific Connections
The Connector IPs list provides a consolidated view of all active Gainsight connections and their IP allow list configurations. From this tab, admins can quickly see which connections have IP restrictions configured and which do not.
The IP allow list at the connector level restricts API access to specific IP addresses for individual connections. This is useful when admins want to limit API access without restricting the entire application.
For more information on how to add a trusted IP to the connector, refer to the Connections List Page article.

The following table describes the different IP Addresses in the Connector IPs page.
| IP Addresses | Descriptions |
| Any | Any IP address can access information; this occurs when no IP address is added in the Connector configuration. |
| Gainsight IPs | Only Gainsight IPs can access information. |
| Specific IPs | Only those trusted IPs configured and Gainsight IPs can access information that is added in the Connectors configuration. |
The following table describes the IP allow list requirement for each connection type.
| Connection Type | Authentication | IP Allow List |
| Gainsight APIs (including Bulk APIs) | Access Key | Mandatory |
| Gainsight Managed S3 | Access Key | Mandatory |
| Gainsight APIs (M2M) | OAuth | Optional |
| User Auth (OAuth) | OAuth | Optional |

- Gainsight enforces access restrictions for Connectors at the IP address level only. Each IP address in the allow list must be a publicly routable IPv4 or IPv6 address.
- VPC Endpoints are not supported. If your traffic originates from within a private VPC, for example, when connecting to a Gainsight Managed S3 bucket, requests without a publicly routable IP will be blocked. To work around this, deploy a NAT Gateway with a static Elastic IP (EIP) in your VPC so that outbound traffic egresses through a stable public IP address. You can then add that Elastic IP to the Gainsight allow list.
How Application and Connector IP Ranges Work Together
When both application-level and connector-level IP ranges are configured, Gainsight combines them using OR logic. An incoming API request is allowed if the source IP matches either the application-level list or the connector-level list for that specific connection.
The following table illustrates how IP validation works when both levels are configured.
Example: Application-level IPs: A, B, C | Connection 1 IP: D | Connection 2 IP: E
| Request | Result | Reason |
| API call using Connection 1 key, from IP A | Allowed | IP A matches the application-level list |
| API call using Connection 1 key, from IP D | Allowed | IP D matches Connection 1 list |
| API call using Connection 2 key, from IP D | Blocked | IP D is only in Connection 1, not in the application-level list or Connection 2 |
| API call using Connection 1 key, from IP E | Blocked | IP E is only in Connection 2, not in the application-level list or Connection 1 |
If no Application IPs are configured, only the connection-level IPs are validated for that specific connection
Supported IP Formats
The following table lists the IP formats supported for both application-level and connector-level IP allow lists.
| Format | Example |
| IPv4 CIDR | 203.0.113.0/24 |
| IPv6 CIDR | 2001:db8::/32 |